How Crypto Works Differently From Standard Vigenere Cipher
Cryptography is the practice of secure communication in the presence of third parties. Cryptography is a fundamental security technology used in a variety of applications from email and web browsing to secure communications, authentication, and data integrity.
Cryptography works by transforming readable text into an unreadable format called cipher text. The cipher text can only be read by someone who knows the encryption algorithm and the key.
Cryptography is based on two principles: symmetric-key cryptography and public-key cryptography. Symmetric-key cryptography is based on the same key that is used to encrypt and decrypt data. The key is stored with the data and is only used to encrypt the data. The key is never used to decrypt the data.
Public-key cryptography is based on two keys. The public key is used to encrypt data. Anyone can send data that they want encrypted using the public key. The recipient can only decrypt the data using the private key. The private key is only known to the recipient and the encryption algorithm.
Cryptography is used to protect data from being accessed by unauthorized individuals. It is also used to verify the identity of a sender and to ensure that data is received by the intended recipient.
The Benefits of Using Crypto Over Standard Vigenere Cipher
Cryptography is the process of secure communication in the presence of third parties. Cryptography is a mathematical science used to protect information from unauthorized access. Cryptography can be used in a variety of applications such as secure communications, data encryption, digital signatures, and authentication.
The benefits of using cryptography over standard Vigenere cipher are:
-Cryptography is more secure: Cryptography uses mathematical algorithms to secure data. Standard Vigenere cipher is not as secure as cryptography because it relies on the use of a key. If the key is revealed, the cipher can be deciphered.
-Cryptography is more reliable: Cryptography is more reliable because it is difficult to break. A standard Vigenere cipher can be easily broken if the correct key is known.
-Cryptography is faster: Cryptography is faster because it uses mathematical algorithms to encrypt and decrypt data.
The Disadvantages of Using Standard Vigenere Cipher Over Crypto
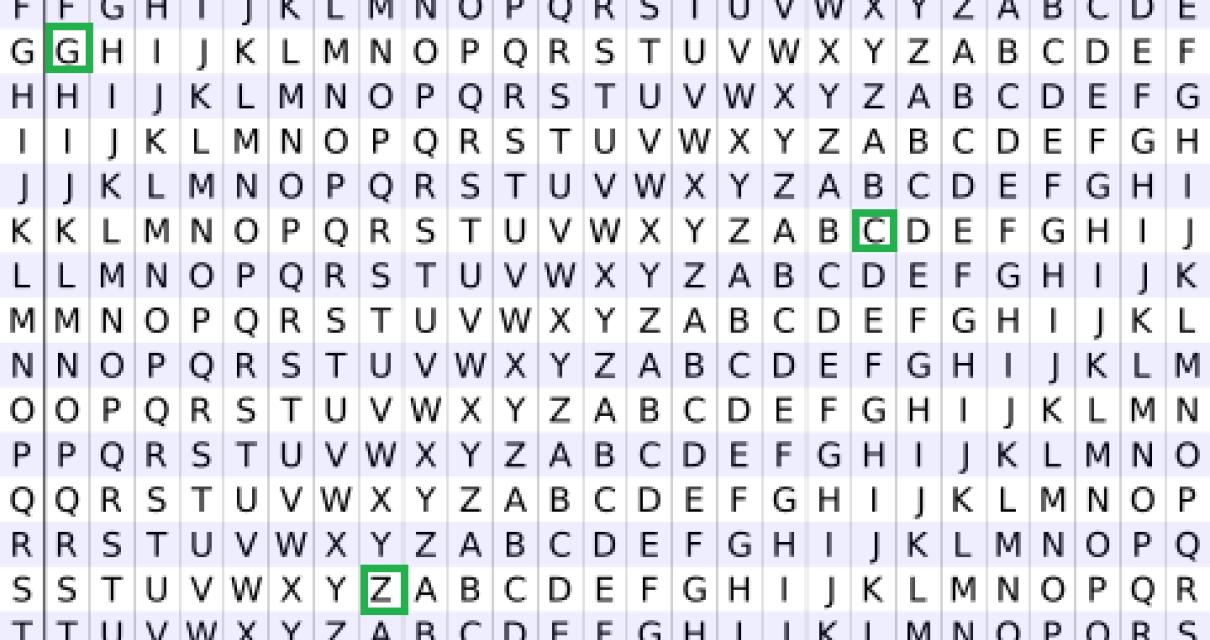
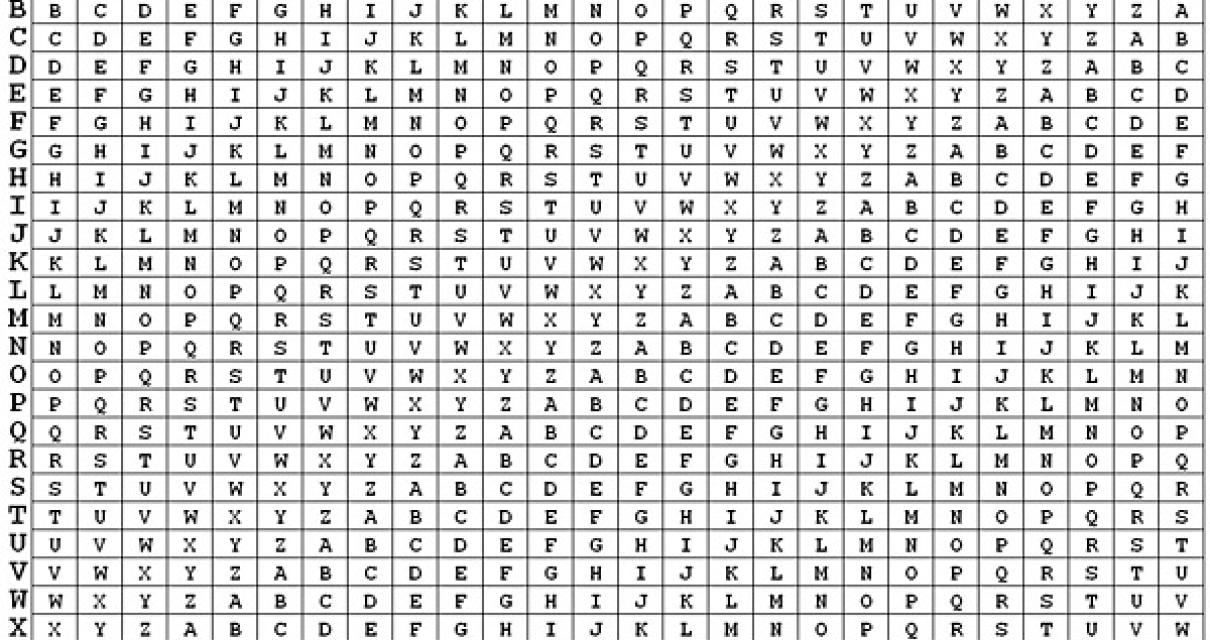
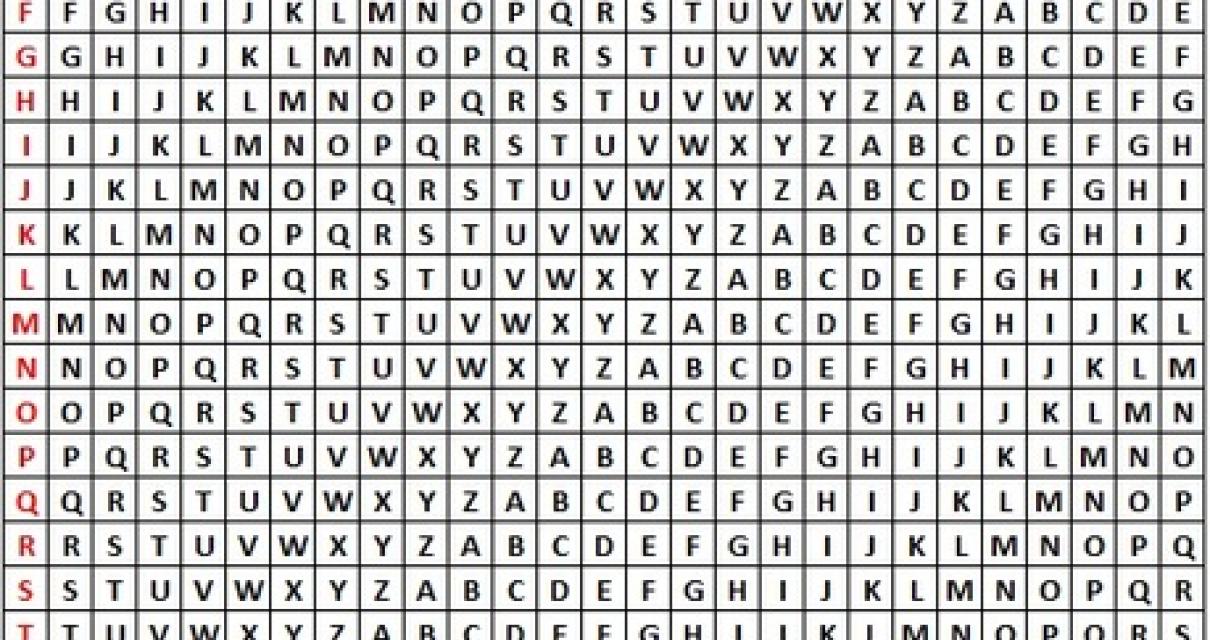
Vigenere
There are a few potential disadvantages of using a standard Vigenere cipher over a crypto Vigenere cipher. First, a standard Vigenere cipher is easier to crack than a crypto Vigenere cipher. Second, standard Vigenere ciphers are less secure than crypto Vigenere ciphers. Finally, standard Vigenere ciphers are less efficient than crypto Vigenere ciphers.
Why Crypto is the More Secure Option
There are a few different factors that can help to determine which option is more secure: the type of cryptography used, the location of the data, and the security measures in place.
Cryptography is a technology that helps protect data from being accessed by unauthorized individuals. Cryptography can be used to protect the data in transit, at rest, or in the cloud. Some of the most common types of cryptography include symmetric-key cryptography, which uses the same key to encrypt and decrypt data, and asymmetric-key cryptography, which uses two different keys.
Location is another factor that can be considered when determining which option is more secure. If the data is located in a centralized location, such as on a server, it is more vulnerable to attack. If the data is located in a decentralized location, such as on a blockchain, it is more secure.
Lastly, security measures can be put in place to help protect the data from being accessed by unauthorized individuals. These measures may include firewalls, encryption, and access controls.
How Crypto Can Help You Stay Safe Online
Cryptocurrencies are digital or virtual tokens that use cryptography to secure their transactions and to control the creation of new units. Cryptocurrencies are decentralized, meaning they are not subject to government or financial institution control.
Cryptocurrencies are unique in that they allow for quick and easy transactions without the need for a middleman, such as a bank. This makes them an attractive option for online transactions, as there is less risk of fraud or theft.
Some of the most popular cryptocurrencies include Bitcoin, Ethereum, and Litecoin. Cryptocurrencies are not backed by any physical assets, but by trust in the security and legitimacy of the code and network.
While cryptocurrencies are not legal tender, many governments are beginning to recognize their potential and are beginning to experiment with regulations surrounding them. In some cases, such as China, authorities have banned all cryptocurrencies outright. In other cases, such as Venezuela, authorities have imposed strict controls on how cryptocurrencies can be used.
Overall, cryptocurrencies offer a number of advantages over traditional forms of payment, making them an attractive option for online transactions. While they may not be legal tender, they are still accepted by many merchants and can provide a safer way to store your assets.
Tips for Using Crypto to Keep Your Data Secure
There are a few things you can do to keep your crypto assets safe and secure:
1. Use a hardware wallet.
A hardware wallet is a type of hot wallet that stores your coins offline on a physical device. This helps to protect your coins from hackers who might be able to steal them if they get access to your computer or mobile device.
2. Use a strong password.
Make sure you create a strong password that is unique to you and your wallet. Don't use easily guessed words or easily accessible information like your birth date or email address.
3. Store your coins in a secure location.
Keep your coins in a secure location, preferably offline. This means avoiding online wallets and exchanges where your coins could potentially be stolen.
4. Don't share your private keys.
Never share your private keys with anyone. This means never transferring coins to someone else in exchange for goods or services, and never leaving them stored on any online platform.
The Risks of Not Using Crypto
There are several risks associated with not using crypto. The first is that you may be missing out on potential investment opportunities. Cryptocurrencies are still relatively new and there is a lot of speculation involved, which means that prices can be volatile. If you don't want to risk your investment, it may be best to stay away from crypto altogether.
Another risk is that you may be vulnerable to cybercrime. Cryptocurrencies are often stored on online platforms, which means that they are at risk of being stolen. If your crypto is stolen, it may be difficult to get it back. This is especially a concern if you don't have a secure password or encryption certificate.
Finally, not using crypto could also lead to financial instability. If the global economy goes bad, there is a chance that crypto values will fall as well. This could leave you with a loss in your investment.
How to Use Crypto to Protect Your Privacy
There are a few ways to use crypto to protect your privacy.
1. Use a privacy-focused cryptocurrency like Monero or Zcash. These cryptocurrencies are designed to keep your transactions private, and they're not subject to the same kinds of government surveillance as regular currencies.
2. Use a VPN to encrypt your internet traffic. This will protect your browsing history and other personal information from being tracked by third-party companies or governments.
3. Use a secure messaging service like Signal or WhatsApp to communicate with friends and family without revealing your personal information.
4. Use a privacy-focused browser like Firefox or Opera. These browsers are designed to keep your online activity private by encrypting your traffic and blocking third-party websites from tracking your online activity.
Why Crypto is the Future of Data Security
Crypto is the future of data security. Not only is it more secure, but it’s also cheaper and faster. With crypto, you can keep your data safe without having to pay high fees. Additionally, blockchain technology makes it extremely difficult for anyone to tamper with your data.